Disclaimer: We have not performed any live investigation. This was a part of our university assignment, wherein we assumed the roles of forensics investigator, determining what methods were applicable. You are welcome to come up with your own findings and resolve the case. We attempted to follow the global methodology, illustrating what a basic forensics investigation report should look like. Credits Edmand Dester Thipursian – Edmand.dester@gmail.com Sai Thogarcheti – Harikamurthy9@gmail.com Abdullah Al Fahad – candyman961@hotmail.com Chintan Gurjar – chintangurjar@outlook.com Adam Mentsiev – adam.mentsiev@study.beds.ac.uk Alams Titus Mammuan – alamsx11@gmail.com 1.
Introduction Computer technology is the major integral part of everyday human life, and it is growing rapidly, as are computer crimes such as financial fraud, unauthorized intrusion, identity theft and intellectual theft. Mixvibes Cross V1 5 0 Cracked Rib. To counteract those computer-related crimes, Computer Forensics plays a very important role. “Computer Forensics involves obtaining and analysing digital information for use as evidence in civil, criminal or administrative cases (Nelson, B., et al., 2008)”. Computer Forensics Boot Camps A Computer Forensic Investigation generally investigates the data which could be taken from computer hard disks or any other storage devices with adherence to standard policies and procedures to determine if those devices have been compromised by unauthorised access or not.
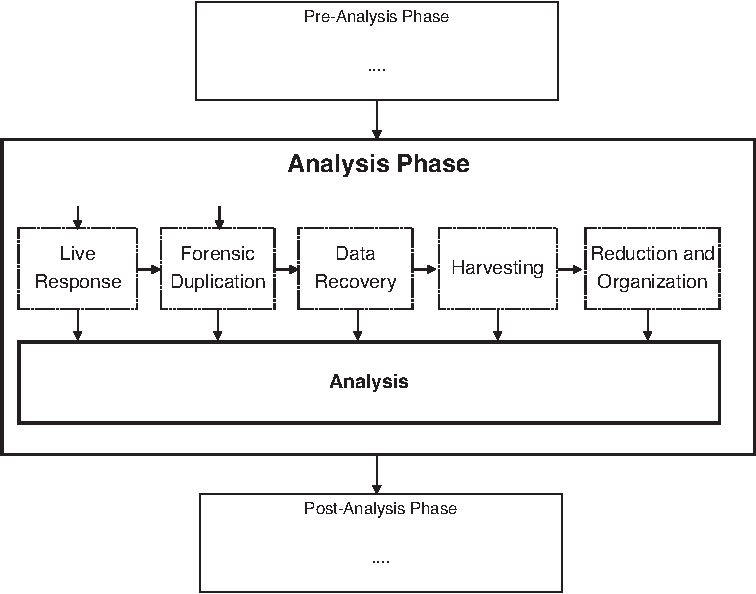
Taboo Game Wedding Version Song on this page. Computer Forensics Investigators work as a team to investigate the incident and conduct the forensic analysis by using various methodologies (e.g. Dead End Shambhala Rar. Static and Dynamic) and tools (e.g. ProDiscover or Encase) to ensure the computer network system is secure in an organization.
We are delighted to announce the arrival of PDF Drive. Computer Forensics: Investigation Procedures. Computer Forensics: Investigating Network Intrusions. Incident Response and Computer Forensics 2nd ed..pdf - Free. Investigation Procedures and Response.
Most Viewed Articles
- Forza Motorsport 4 Keygen Photoshop
- Ch Reloading Presses Manually
- Joiner Avi Free Download Crack For Gta
- Microsoft Office 2003 Language Patch Italy Flag
- Download Cisco Router Ios Image Gns3 Academy
- How To Shoot Video That Doesn`t Suck - Steve Stockman.epub
- Blu Ray Xp Driver 5 3 0 1 X86 Servers
- Fire Emblem Souen No Kiseki Isolation
- Applied Calculus 9th Edition Tan Pdf Free
- Free Download Laura Marling Alas Rapidshare Programs Like Limewire
- Hotspot Shield 3.42 Crack Free Download
- Test Tools For Companies