
By By June 8, 2012 If there’s one thing that the LinkedIn, eHarmony and now hacks have taught us in the past week, it’s that people are really bad at picking secure passwords. As a lot of people used the phrase “link” in their LinkedIn passwords — not exactly a high hurdle for someone intent on cracking your credentials. The second-most popular phrase? “1234.” I get it.
There have been a lot of times when I’ve used a simple password to sign up for a service, just to get through the registration process quickly. And trying to come up with strong passwords is awful.
As my wrote Thursday, password tips are often unhelpful because they offer codes that are impossible to remember. Last week, I spoke to Chet Wisniewski, senior security adviser for Sophos, about that found 79 percent of those surveyed used different passwords for online accounts.
He said that was encouraging but that the average person shouldn’t stop there. Most people who use multiple passwords, he said, seem to take a tiered approach: Say, one really secure password that they use for their bank and a throwaway password for quick commenting or blogging services.
I had a very big surprise with this dump because when I started to work on it, I quickly noticed that all password were uppercased Thanks eHarmony!
What most don’t realize, he said, is that a throwaway password often includes important information that can be used to access a more secure account. Using your mother’s maiden name or kid’s birthday in your lowest-tier password? Make sure those aren’t the answers to the security questions you need to get into your bank account. Or that they aren’t on your Facebook profile. What’s important to remember, even if you can’t keep track of a different password for every account, is that you shouldn’t ever use the same password for accounts that you use every day.
That means, Facebook and Gmail should have different passwords, which in turn should be different from your LinkedIn, Spotify, Pandora, Twitter or, goodness forbid, your bank. Hackers are unlikely to target you, specifically, but if one of your passwords gets into a major data dump, you’re just opening the door for them if you’re sharing passwords. Wisniewski said that people should still be creating unique passwords for each account, and that maybe people should think about being a little less truthful on their security questions, as well, just as a precaution. Lineage 1 Bot Program For Chatting.
Name, for example, your second car and not your first, or your child’s high school mascot. I have a whole bunch of tricks that I use to insert numbers, symbols, caps and general confusion into my passwords in a way only I will remember. But with the number of services I subscribe to, I still find myself trying to remember if I replaced that one letter of my first-grade teacher’s last name with a “1” or a “!” or if I opted for a different reference from my past altogether. One tip I do like: Pick something personal, and type it shifted one key to the right. Even that, though, will become less secure if people still use the same common passwords — like “password” — and people begin trying “[sddeptf” to hack your accounts, too. In any case, everyone should be extra wary of strange e-mails — particularly those with attachments and external links — since fake “phishing” messages will likely be on the rise.
Dear eHarmony, Blow me, you. Yet Another Reason Why eHarmony Sucks. I know I entered the wrong password enough times for you to dump me into the “password. ALL FALL DOWN — eHarmony confirms its members’ passwords were posted online, too Vague post leaves unanswered questions about dump of 1.5 million passwords.
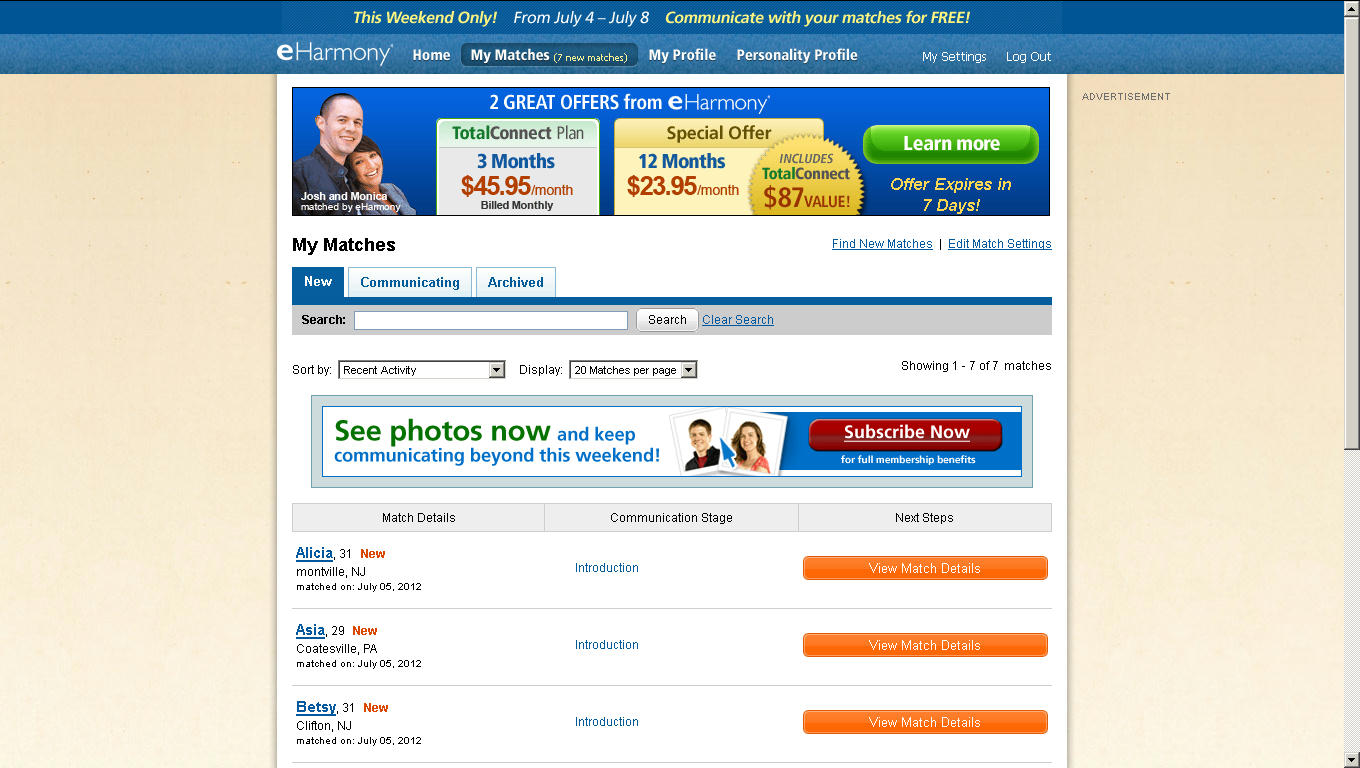
Share this story Online dating site eHarmony has confirmed that a massive list of passwords posted online included those used by its members. 'After investigating reports of compromised passwords, we have found that a small fraction of our user base has been affected,' company officials said in a. The company didn't say what percentage of 1. Etica Ministerial Joe E Trull Pdf Editor more. 5 million of the passwords, some appearing as MD5 cryptographic hashes and others converted into plaintext, belonged to its members. The confirmation followed a that a dump of eHarmony user data preceded a separate dump of LinkedIn passwords. EHarmony's blog also omitted any discussion of how the passwords were leaked. That's unsettling, because it means there's no way to know if the lapse that exposed member passwords has been fixed.
Most Viewed Articles